Information Systems Management > QUESTIONS & ANSWERS > CISSP: Unit 3: Security Engineering, Questions with accurate answers, 100% Accurate, rated A+ (All)
CISSP: Unit 3: Security Engineering, Questions with accurate answers, 100% Accurate, rated A+
Document Content and Description Below
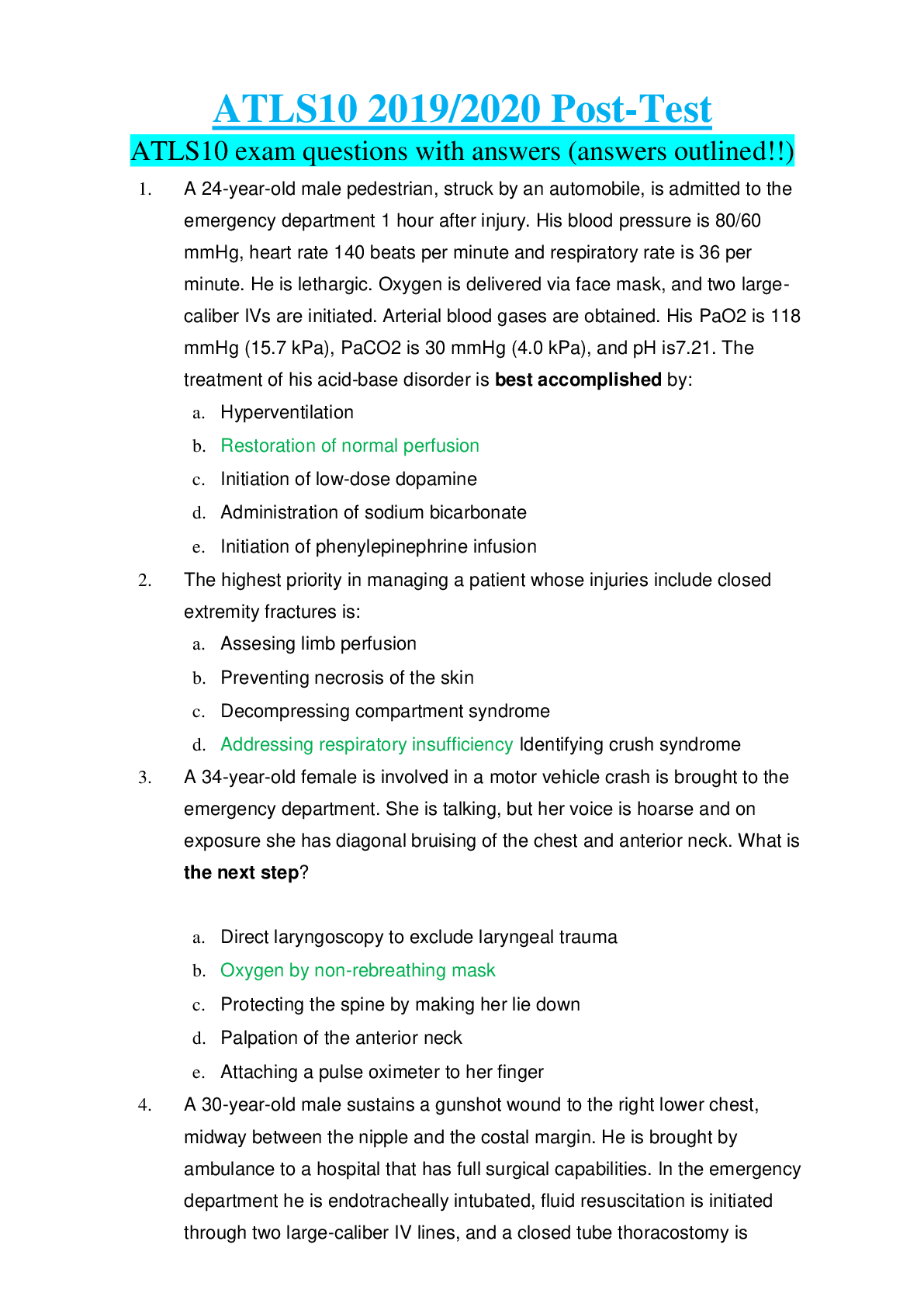
CISSP: Unit 3: Security Engineering, Questions with accurate answers, 100% Accurate, rated A+ Abstraction - ✔✔-Involves the removal of characteristics from an entity in order to easily repres... ent its essential properties. Access Control Matrix - ✔✔-A two-dimensional table that allows for individual subjects and objects to be related to each other. Asymmetric Algorithms - ✔✔-One-way functions, that is, a process that is much simpler to go in one direction (forward) than to go in the other direction (backward or reverse engineering). Address Space Layout Randomization (ASLR) - ✔✔-Involves randomly arranging the positions of key data areas of a program, including the base of the executable and the positions of the stack, heap, and libraries in a process's memory address space. Aggregation - ✔✔-Combining non-sensitive data from separate sources to create sensitive information. Algorithm - ✔✔-A mathematical function that is used in the encryption and decryption processes. Bell-La Padula Model - ✔✔-Explores the rules that would have to be in place if a subject is granted a certain level of clearance and a particular mode of access. Brewer-Nash (The Chinese Wall) Model - ✔✔-This model focuses on preventing conflict of interest when a given subject has access to objects with sensitive information associated with two competing parties. Cable Plant Management - ✔✔-The design, documentation, and management of the lowest layer of the OSI network model - the physical layer. Certificate Authority (CA) - ✔✔-An entity trusted by one or more users as an authority in a network that issues, revokes, and manages digital certificates. Ciphertext or Cryptogram - ✔✔-The altered form of a plaintext message, so as to be unreadable for anyone except the intended recipients. Cloud Computing - ✔✔-A model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (e.g. networks, servers, storage, applications, and services) that can be rapidly provisioned and released with minimal management. Common Criteria - ✔✔-Provides a structured methodology for documenting security requirements, documenting and validating security capabilities, and promoting international cooperation in the area of IT security. Community Cloud Infrastructure - ✔✔-Provisioned for exclusive use by a specific community of consumers from organizations that have shared concerns. Confusion - ✔✔-Provided by mixing (changing) the key values used during the repeated rounds of encryption. When the key is modified for each round, it provides added complexity that the attacker would encounter. Control Objects for Information and Related Technology (COBIT) - ✔✔-Provides a set of generally accepted processes to assist in maximizing the benefits derived using information technology (IT) and developing appropriate IT governance. Covert Channels - ✔✔-Communications mechanisms hidden from the access control and standard monitoring systems of an information system. Cryptanalysis - ✔✔-The study of techniques for attempting to defeat cryptographic techniques and, more generally, information security services. Cryptology - ✔✔-The science that deals with hidden, disguised, or encrypted communications. It embraces communications security and communications intelligence. Cyber-Physical Systems (CPS) - ✔✔-Smart networked systems with embedded sensors, processors, and actuators that are designed to sense and interact with the physical world and support real-time, guaranteed performance in safety-critical applications. Data Hiding - ✔✔-Maintains activities at different security levels to separate these levels from each other. Data Warehouse - ✔✔-A repository for information collected from a variety of data sources. Decoding - ✔✔-The reverse process from encoding - converting the encoded message back into its plaintext format. Diffusion - ✔✔-Provided by mixing up the location of the plaintext throughout the ciphertext. Digital Certificate - ✔✔-An electronic document that contains the name of an organization or individual, the business address, the digital signature of the certificate authority issuing the certificate, the certificate holder's public key, a serial number, and the expiration date Digital Rights Management (DRM) - ✔✔-A broad range of technologies that grant control and protection to content providers over their own digital media. Digital Signatures - ✔✔-Provide authentication of a sender and integrity of a sender's message. Enterprise Security Architecture (ESA) - ✔✔-Focused on setting the long-term strategy for security services in the enterprise. Firmware - ✔✔-The storage of programs or instructions in ROM. "Generally Accepted Principles and Practices for Securing Information Technology Systems" (NIST SP 800-14) - ✔✔-Provides a foundation upon which organizations can establish and review information technology security programs. Graham-Denning - ✔✔-Primarily concerned with how subjects and objects are created, how subjects are assigned rights or privileges, and how ownership of objects is managed. Inference - ✔✔-The ability to deduce (infer) sensitive or restricted information from observing available information. ISO/IEC 21827:2008, The Systems Security Engineering - Capability Maturity Model (SSE-CMM) - ✔✔- Describes the essential characteristics of an organization's security engineering process that must exist to ensure good security engineering. [Show More]
Last updated: 1 year ago
Preview 1 out of 8 pages

Also available in bundle (1)
CISSP test BUNDLE, QUESTIONS AND ANSWERS, VERIFIED.
CISSP test bank - Exam questions to study/review 1. Top questions with accurate answers, 100% Accurate. VERIFIED.
By Topmark 1 year ago
$36
14
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Mar 14, 2023
Number of pages
8
Written in
Additional information
This document has been written for:
Uploaded
Mar 14, 2023
Downloads
0
Views
57