Computer Architecture > GUIDELINES > Lesson 2.3 – Server Exploits | Download for quality grades | (All)
Lesson 2.3 – Server Exploits | Download for quality grades |
Document Content and Description Below
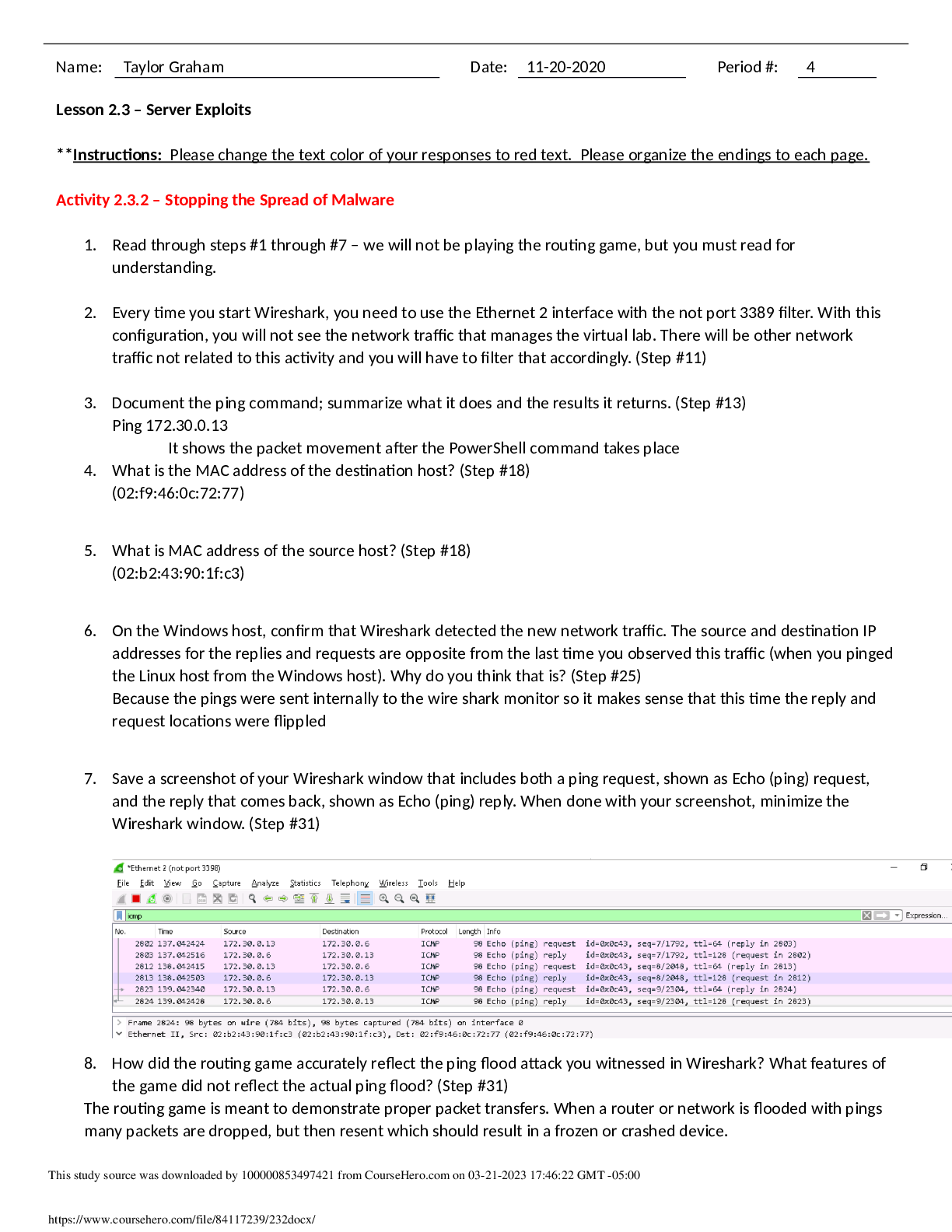
** Instructions: Please change the text color of your responses to red text. Please organize the endings to each page. Activity 2.3.2 – Stopping the Spread of Malware 1. Read through steps #1 thro... ugh #7 – we will not be playing the routing game, but you must read for understanding. 2. Every time you start Wireshark, you need to use the Ethernet 2 interface with the not port 3389 filter. With this configuration, you will not see the network traffic that manages the virtual lab. There will be other network traffic not related to this activity and you will have to filter that accordingly. (Step #11) 3. Document the ping command; summarize what it does and the results it returns. (Step #13) Ping 172.30.0.13 It shows the packet movement after the PowerShell command takes place 4. What is the MAC address of the destination host? (Step #18) (02:f9:46:0c:72:77) 5. What is MAC address of the source host? (Step #18) (02:b2:43:90:1f:c3) 6. On the Windows host, confirm that Wireshark detected the new network traffic. The source and destination IP addresses for the replies and requests are opposite from the [Show More]
Last updated: 1 year ago
Preview 1 out of 2 pages
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Apr 03, 2023
Number of pages
2
Written in
Additional information
This document has been written for:
Uploaded
Apr 03, 2023
Downloads
0
Views
37