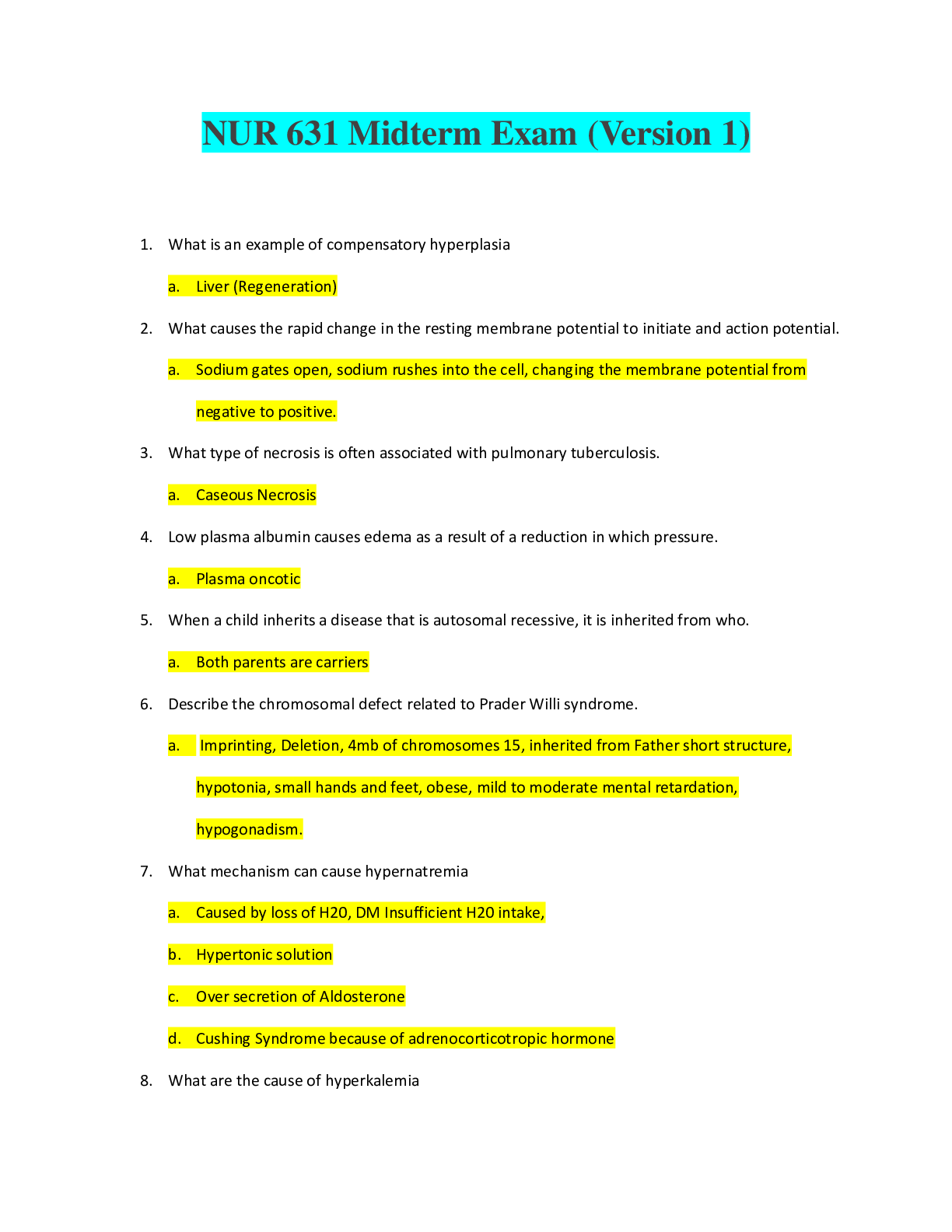
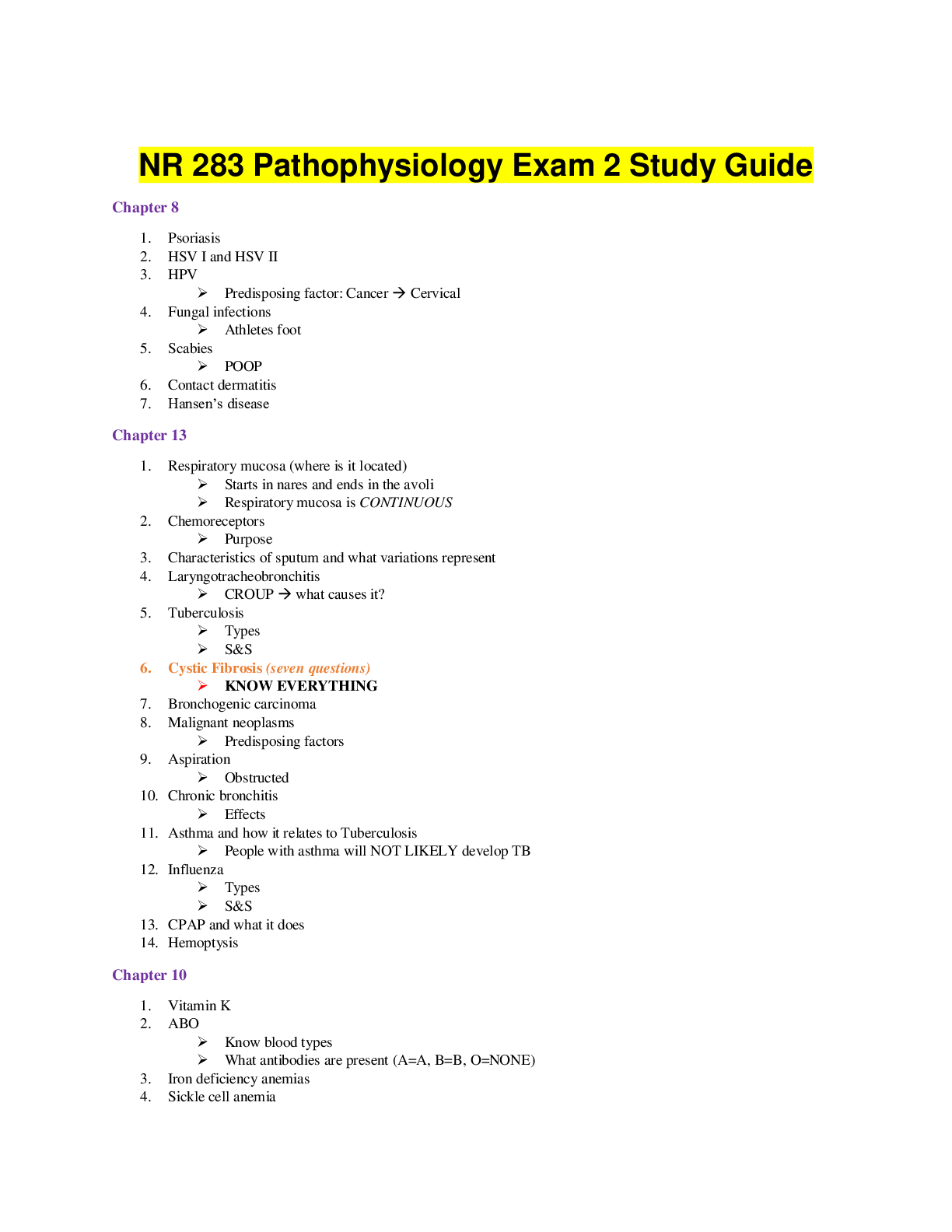
Computer Science > EXAM > SEC 572 Week 8 Final Exam - Latest 2019/20 complete solution guide, Devry. (All)
SEC 572 Week 8 Final Exam - Latest 2019/20 complete solution guide, Devry.
Document Content and Description Below
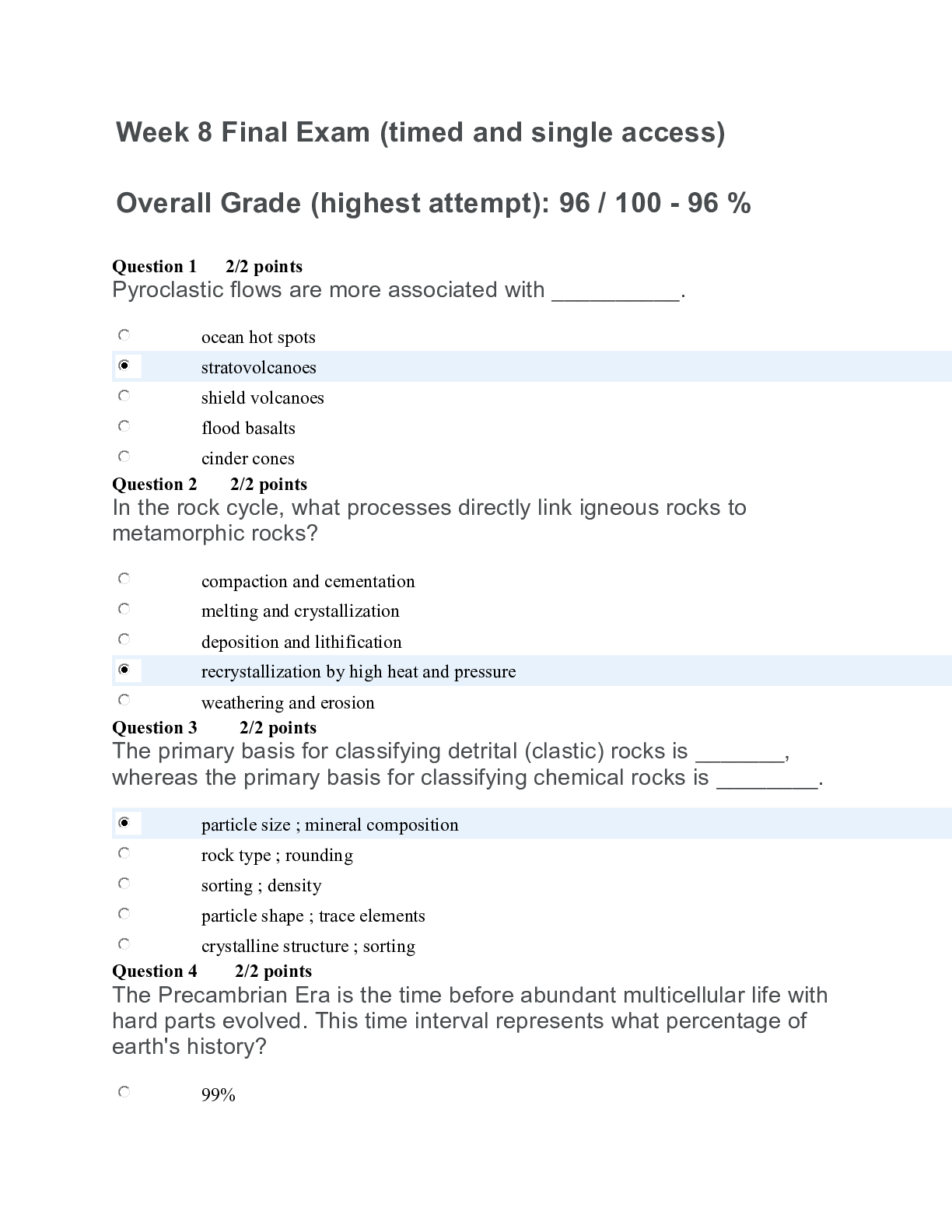
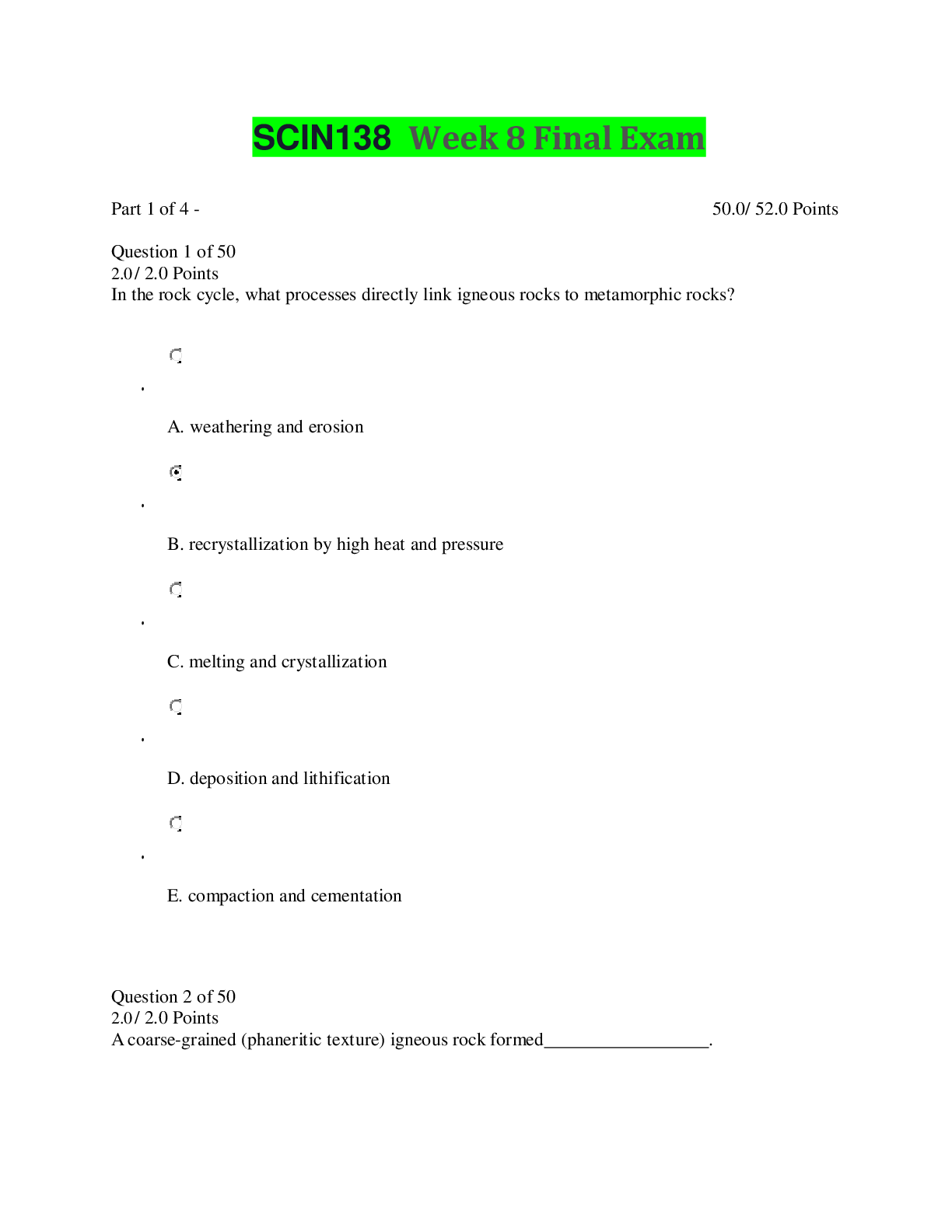
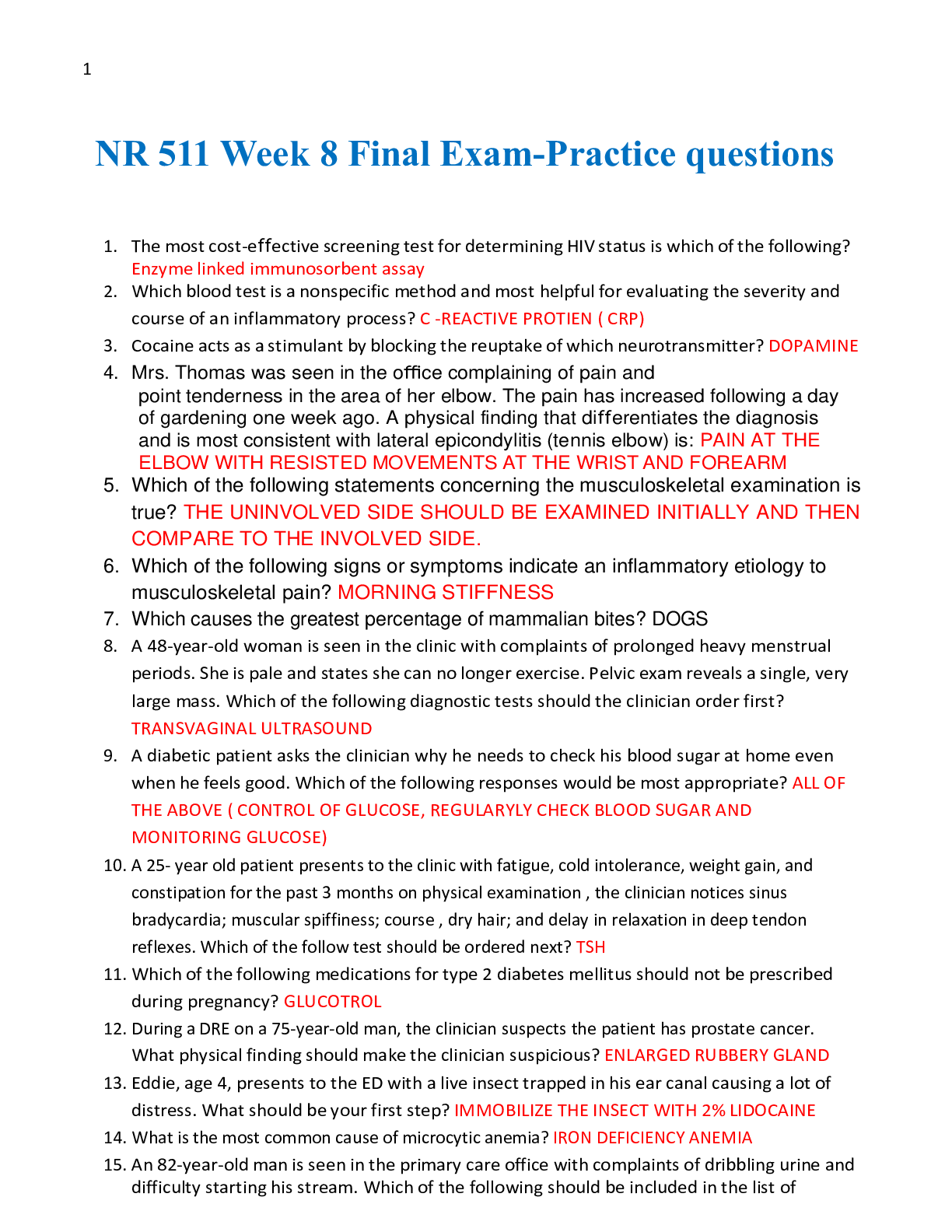
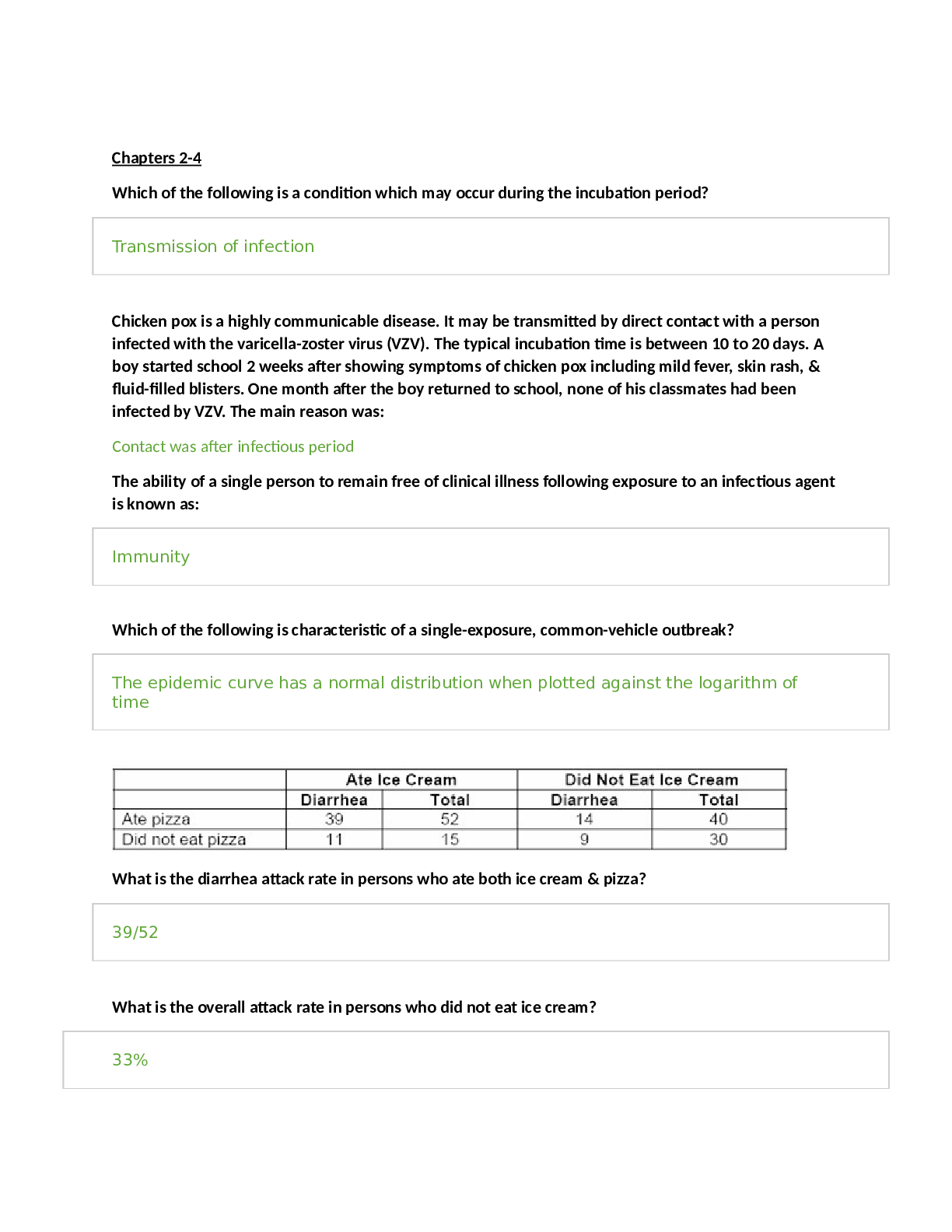
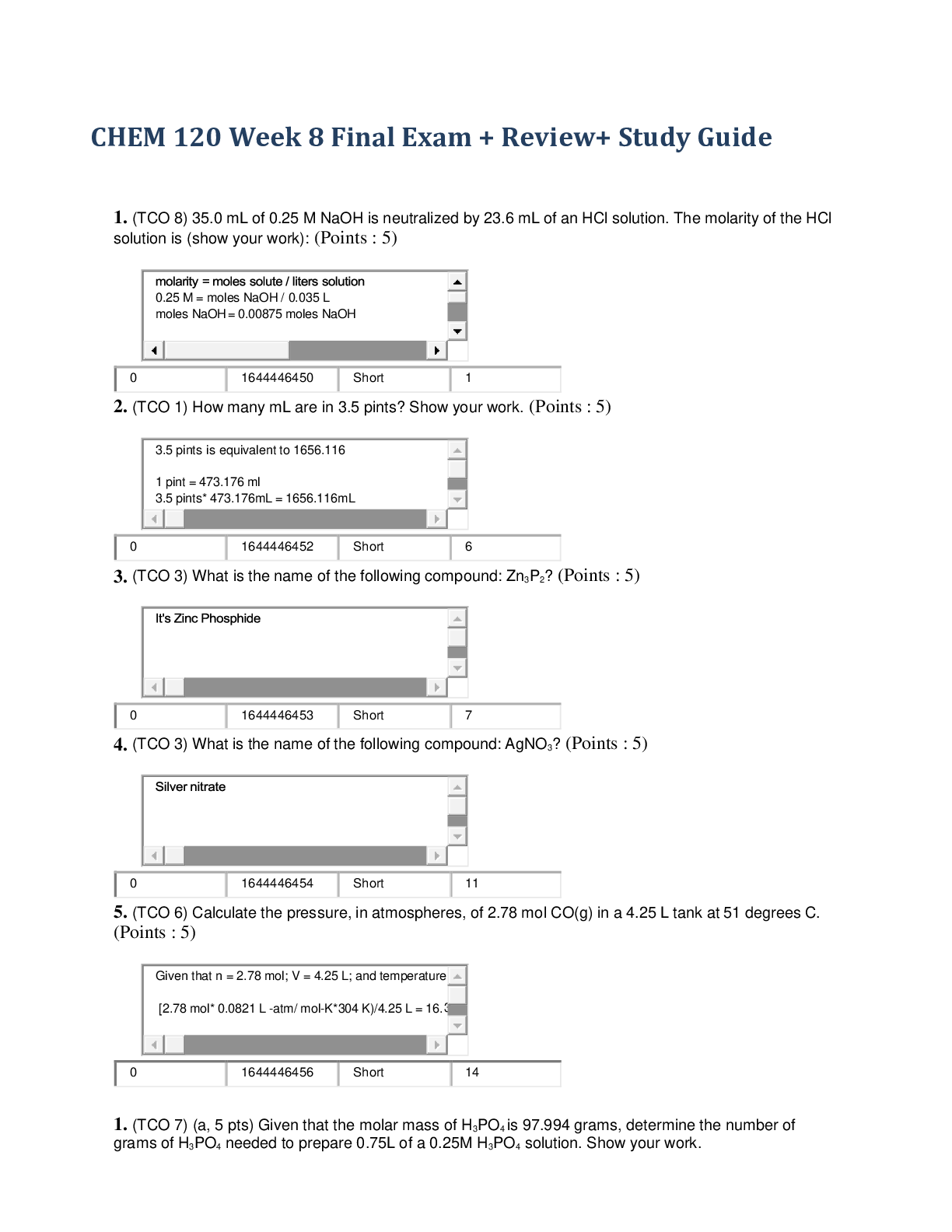
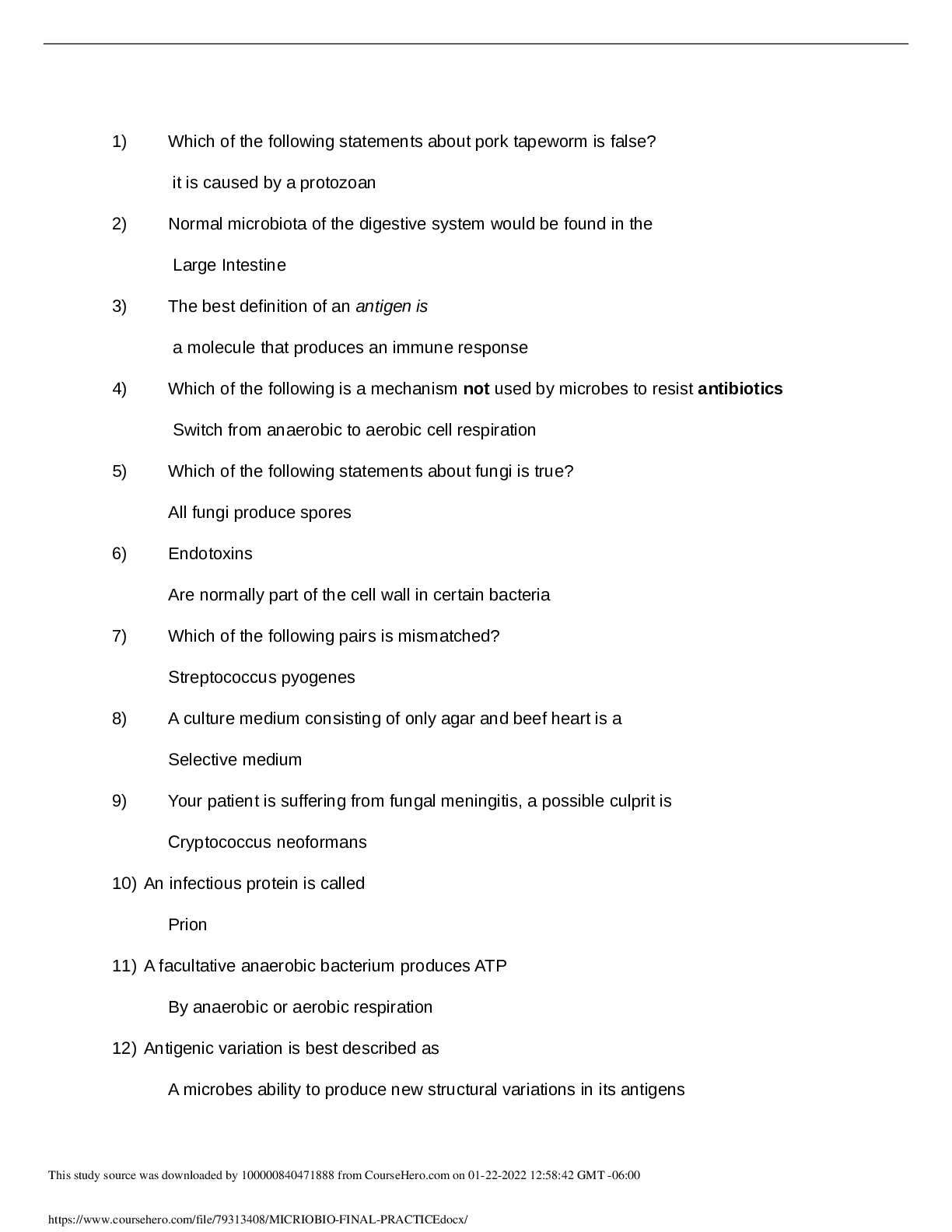
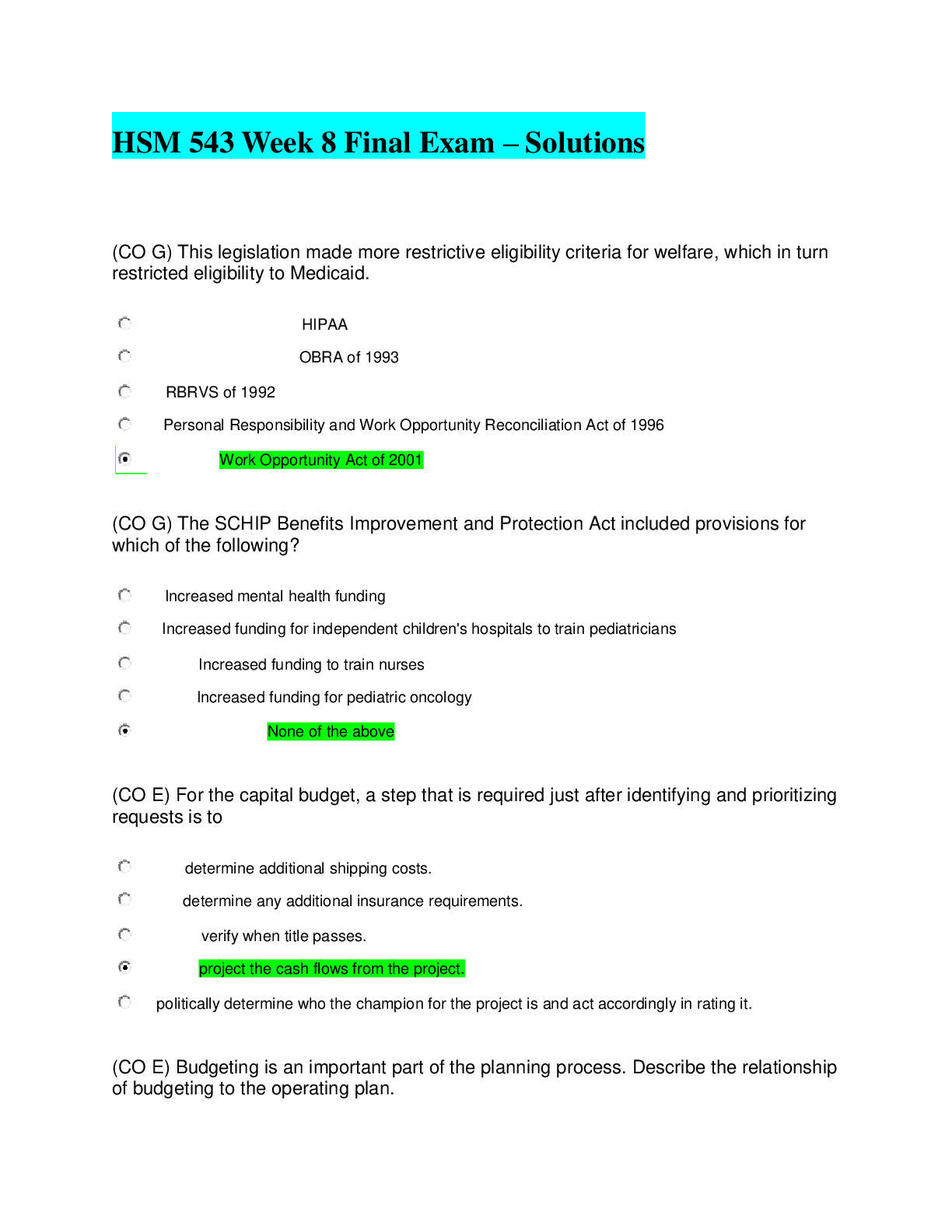
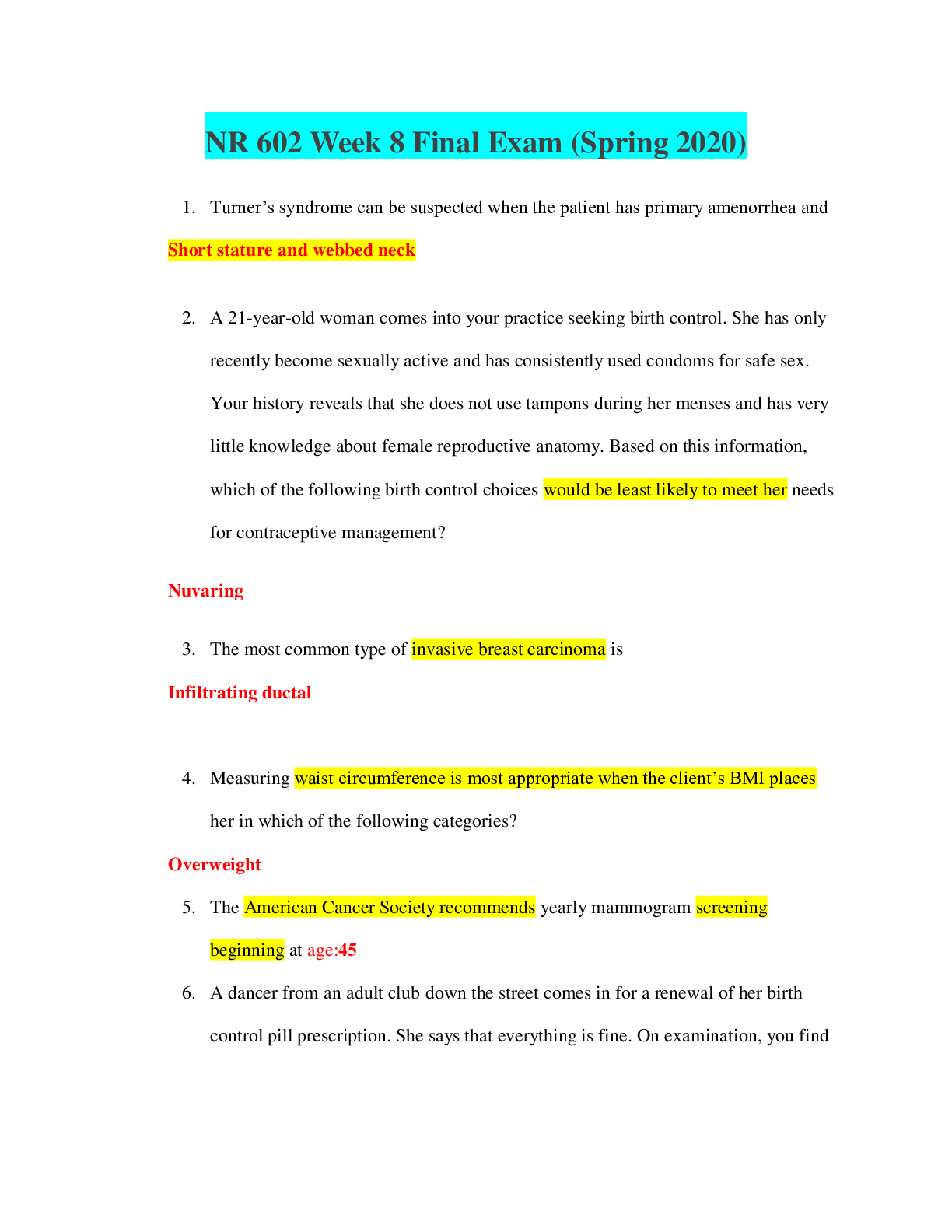
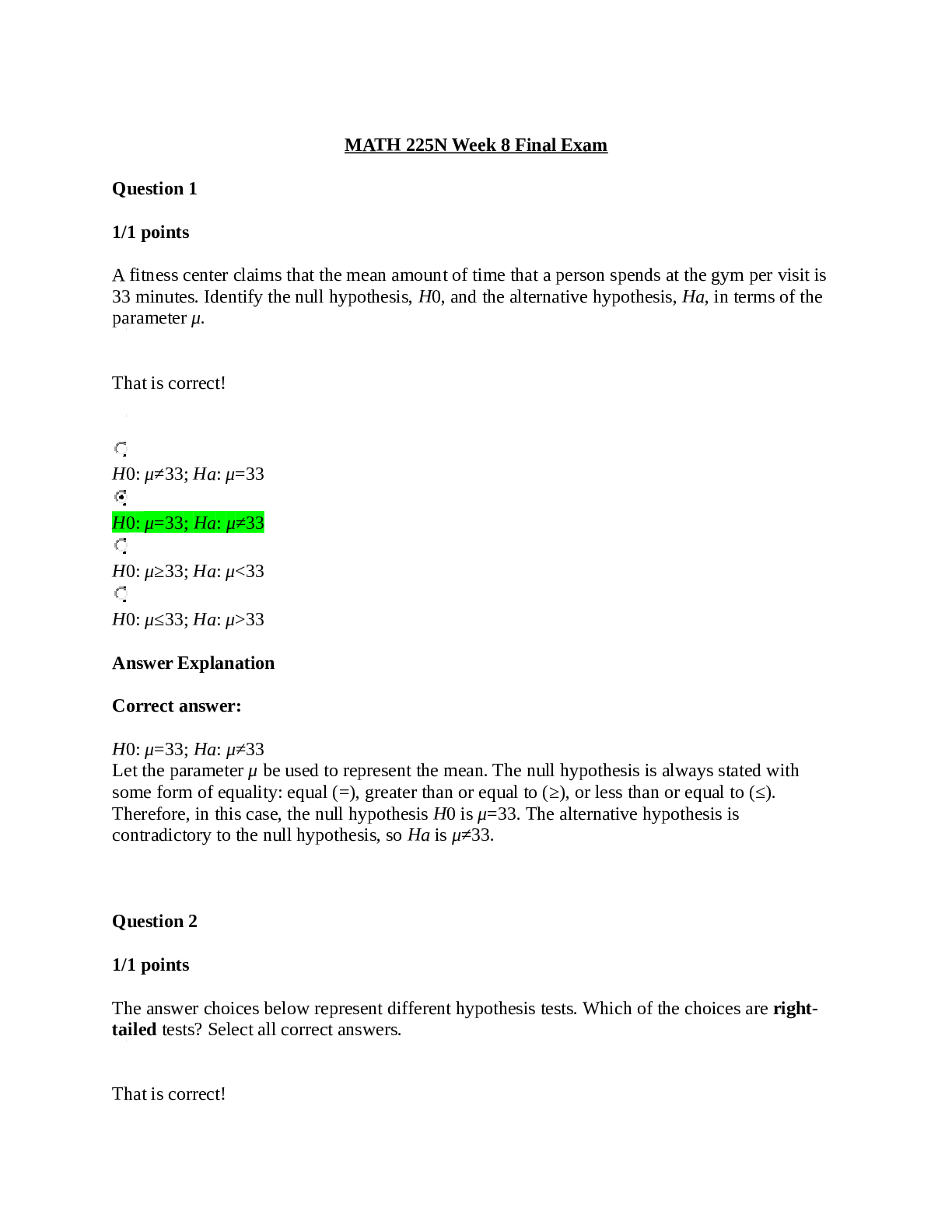
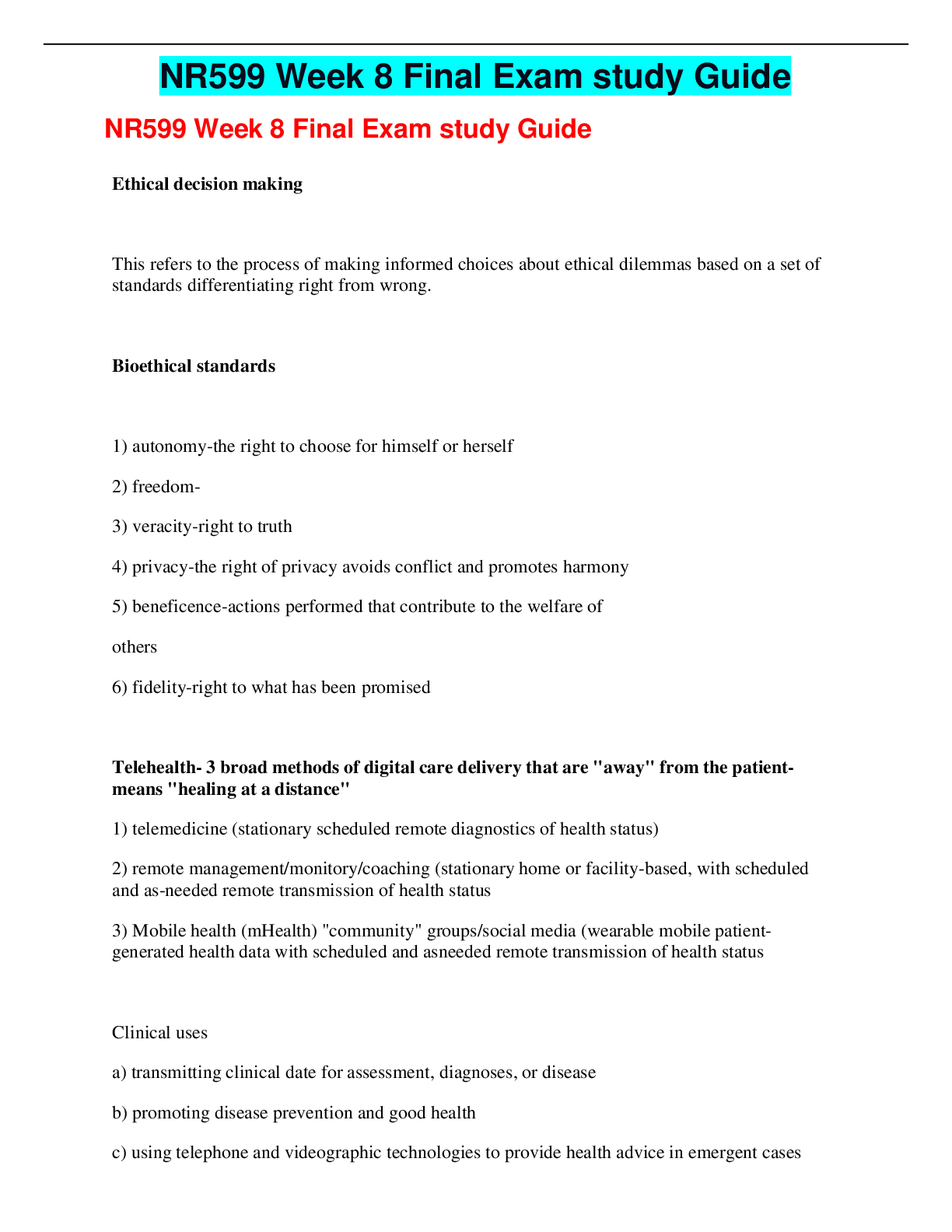
SEC 572 Week 8 Final Exam Question 15 pts (TCO A) During the _____ phase of the attack process, the attacker attempts to look for an easy way in. reconnaissance footprinting scanning ... enumeration Question 25 pts (TCO A) Which is the biggest cause of data loss for most organizations? Hackers Natural disasters User error Hardware failure Question 35 pts (TCO B) When and under what circumstances should you reveal your password to someone? Under no circumstances To IT when they are troubleshooting a problem To anyone who asks for it, and then immediately change it To your supervisor Question 45 pts (TCO B) An extranet provides access to _____. resources for an organization’s suppliers an e-commerce web site personnel policies travel requests Question 55 pts (TCO C) The 3DES algorithm uses _____ separate keys. three four one five Question 65 pts (TCO C) A message-digest algorithm such as MD5 is designed to _____. accept a hash and produce variable output accept a date and generate fixed length output create AES keys rehash a string Question 75 pts (TCO D) A DMZ is used to isolate an interior routing protocol the inside from the outside HIDS a trusted from an untrusted network Question 85 pts (TCO E) With split tunneling, a VPN can connect _____ and _____ in order to not have to place the traffic in the tunnel first. inside; sector VPN; VPN inner; outer public network; private VPN Question 95 pts (TCO F) To achieve better security, WPA is an improvement on _____. frequency stability key management and authentication 64 K or 128 K bit static secret key SSID beacon frame channelization Question 105 pts (TCO G) The three basic attack vectors are internal, external, and _____. internal external physical security outside in protected mode (TCO A) Discuss the following. (a) How does a man-in-the middle attack objective differ from a distributed denial-of-service (DDoS) attack objective? (b) What are the similarities? (c) How are each of the attacks mitigated? (TCO A) What is the purpose of footprinting? (TCO B) Explain how a TCP/SYN attack works and what can be done about it. (TCO B) What are three things you should keep in mind when writing or reviewing a security policy? (TCO C) When a device performs a stateful packet inspection, what characteristics in a packet’s header are inspected, and why are they important? (TCO D) What is a DMZ? What is it used for? (TCO E) What are the three types of VPNs? Describe the characteristics of each one. (TCO F) What is a rogue access point and what is it used for? (TCO G) Define firewalking. (TCO B) Discuss the security problems faced by TJX Companies. [Show More]
Last updated: 1 year ago
Preview 1 out of 9 pages

Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Mar 06, 2020
Number of pages
9
Written in
Additional information
This document has been written for:
Uploaded
Mar 06, 2020
Downloads
0
Views
58





.png)