Military Science > QUESTIONS & ANSWERS > Joint Staff Counterintelligence Awareness and Reporting (CIAR) - Navy FY19 Already Passed (All)
Joint Staff Counterintelligence Awareness and Reporting (CIAR) - Navy FY19 Already Passed
Document Content and Description Below
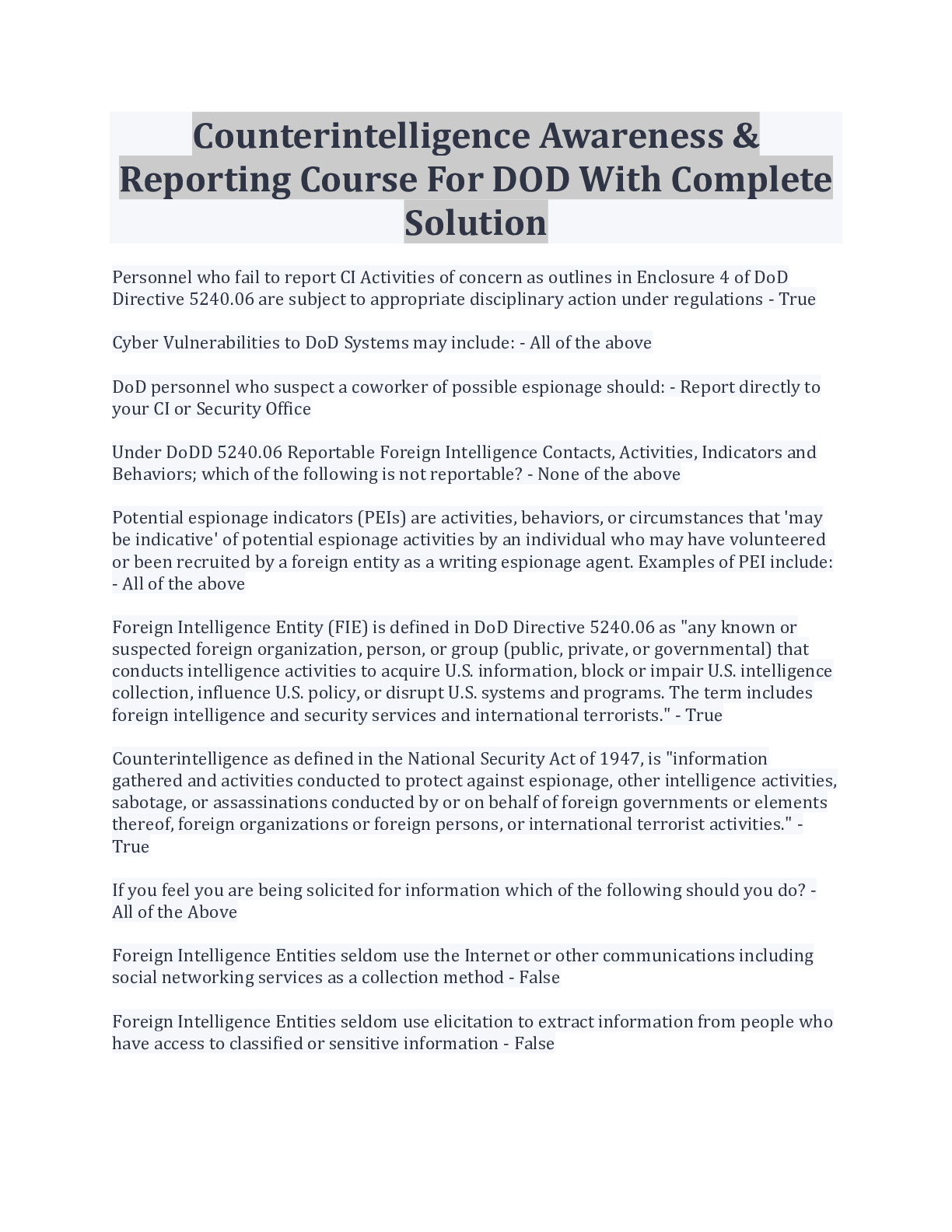
Joint Staff Counterintelligence Awareness and Reporting (CIAR) - Navy FY19 Already Passed Select all that apply. Counterintelligence (CI) pre- and post-foreign travel briefs support you by providi... ng (Course Introduction, Page 3) ✔✔Travel area intelligence and security practices and procedures Information on local and regional threat environments Defensive actions needed to defeat threats Reportable activity guidelines Communicating information about the national defense to injure the U.S. or give advantage to a foreign nation is called (Lesson 1: Foreign Intelligence Entities (FIE), Page 4) ✔✔Espionage It is acceptable to discuss sensitive information such as travel plans in taxis, buses, or other public transportation while traveling in foreign countries. (Lesson 4: Traveling in a Foreign Country, Page 3) ✔✔False Terrorist organizations are considered Foreign Intelligence Entities by the U.S. (Lesson 1: Foreign Intelligence Entities, Page 1) ✔✔True Unclassified information can be collected to produce information that, when put together, would be considered classified. (Lesson 1: Foreign Intelligence Entities, Page 3) ✔✔True All requests to transport media back to the U.S. on behalf of a foreign country must be reported to your Counterintelligence representative. (Lesson 5: Reporting Requirements, Page 1) ✔✔True Foreign adversary use of social networking services causes which of the following concerns? (Select the best answer) (Lesson 3: Internet and Social Networking Services, Page 3) ✔✔All of the answers are correct Human intelligence (HUMINT) targeting methods include which of the following? Select all that apply. (Lesson 1: Foreign Intelligence Entities, Page 8) ✔✔Elicitation Relationship building Cold Pitching Passive collection A foreign power activity or knowledge that is inconsistent with the expected norms that suggest prior foreign knowledge of U.S national security information, processes or capabilities is defined as (Lesson 1: Foreign Intelligence Entities, Page 10) ✔✔Anomaly What percentage of information collected is unclassified? (Lesson 1: Foreign Intelligence Entities, Page 3) ✔✔80-85% Impairment of a Signals Intelligence collection platform or an unexplained compromise of U.S. Intelligence Operations are examples of (Lesson 1: Foreign Intelligence Entities, Page 10) ✔✔An anomaly The Internet and social networking services have allowed (Lesson 3: Internet and Social Networking Services, Page 2) ✔✔All of the above Elicitation can be best described as a guided conversation with a concealed purpose. (Lesson 1: Foreign Intelligence Entities, Page 8) ✔✔True [Show More]
Last updated: 1 year ago
Preview 1 out of 3 pages
Instant download
.png)
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Aug 25, 2022
Number of pages
3
Written in
Additional information
This document has been written for:
Uploaded
Aug 25, 2022
Downloads
0
Views
90

.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)


.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)

